In recent years, the conversation around personal privacy and data security has become intense. With data protection regulations tightening and cybersecurity threats attracting more media attention, users have sought reassurance that their information can be kept out of the wrong hands.
At the same time, there’s been a rise in the popularity of cloud computing. The cloud has had far-reaching impacts, including substantial benefits for businesses and consumers. However, it has changed the game as far as cybersecurity is concerned. Data centers are subject to stringent security requirements to ensure that clients’ data is protected.
Given that cybersecurity is such an important issue among web users, there’s a lot of demand for apps and tools that can offer protection. Software developers and marketers are responding to this increased demand by offering a range of new features and solutions. Cloud computing has been particularly transformative, and so cloud-based solutions are proving to be increasingly popular.

One such tool is the cloud browser. Web browsers are highly vulnerable to cyber criminals, thus putting users at risk of security breaches. Cloud browsers offer web users enhanced security and protection against online fraud, and as such they are attracting a growing audience.
In this guide, we’ll provide a comprehensive and detailed introduction to cloud browsers. We’ll explain how they work and look at what advantages they offer compared to traditional web browsers. Additionally, we’ll explain how RingCentral’s cloud computing security tools can help keep your business – and customers – safe and secure.
Before we do anything else, we’ll start by answering the following question: what is a cloud browser? Let’s take a closer look.
What is a cloud browser?
A cloud browser is, as the name implies, a web browser that uses the capabilities of the cloud to protect users from potential security threats. Rather than hosting the internet browser on your own PC or mobile device, you instead use an app or portal to access an instance of the browser running in the cloud. Cloud browsers are also often referred to as remote browsers, and this gives us an important clue as to how they work.
Why your web browser might be at risk
You may be wondering why there’s so much emphasis on protecting users from the security risks they encounter through their web browsers. The answer is simple: it’s because users come across so many security threats via the browsers they use.
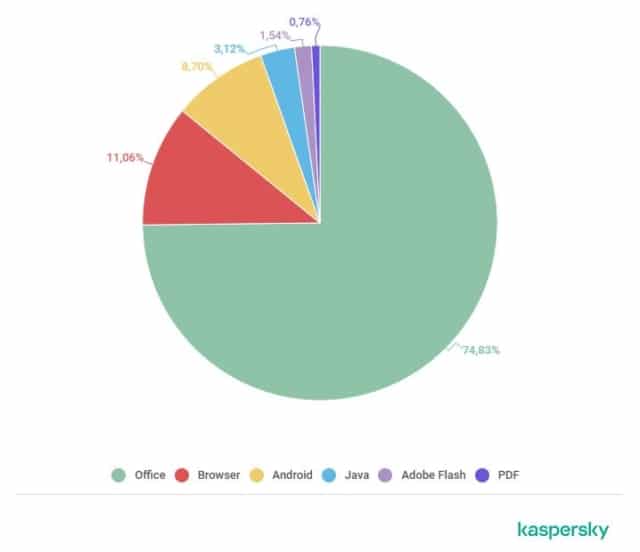
According to data from the first quarter of 2020, the second most common location for exploit attacks – in other words, attacks taking advantage of security vulnerabilities – was a web browser. Ordinarily, non-expert users have a tendency to assume that their browsers and web applications are safe and secure against cybersecurity flaws, but this isn’t the case at all.
There are various security flaws that cyber criminals could exploit. It may be, for instance, that users have downloaded malicious or badly-designed browser extensions, which can be more dangerous than many people appreciate. A particularly interesting risk this year was CookieThief, a trojan on Android designed to steal cookies from mobile browsers in order to provide access to individual’s accounts.
Web browsers such as Google Chrome, Mozilla Firefox, Safari for Mac and Microsoft Internet Explorer have all proved to be vulnerable to security breaches, despite the ongoing attempts of their respective developers to patch up vulnerabilities.
It was hoped that the arrival of HTTPS authentication (which is encrypted in order to enhance data security) in the mid-1990s would mark a decisive improvement in protecting users from online security risks. To an extent, it did, but even today, many websites do not offer HTTPS protection. Other sites, meanwhile, may have faulty HTTPS certificates.
Hackers and other malicious actors are always looking for vulnerabilities to exploit. With the proliferation of browser extensions in recent years, they have more opportunities than ever before. This is one reason why so many users are turning to cloud browsers.
Examples of cloud browsers
There are, as we’ve noted, a number of different cloud browsers for users to choose from. These include browsers such as Maxthon, Puffin and Silo. There are also other, non-freeware alternatives that require users to pay a recurring subscription fee; this is because the providers provide system resources and process traffic themselves.
Perhaps the best known of all the cloud browsers, Maxthon, is a Chinese-developed freeware cloud browser. It is available for Windows, macOS and Linux, while its Maxthon Mobile browser can be used on iOS and Android, as well as Microsoft Windows Phone 8.
In terms of functionality it is quite basic, but it includes the typical features you’d generally expect from a web browser like HTML5 support, bookmarks and tabbed browsing. Its real selling point, as with other cloud browsers, is the enhanced security it offers. Let’s take a look at what other benefits they offer.
Benefits of a cloud browser
So, we’ve given a quick overview of what cloud browsers are, and why ordinary web browsers can be a serious security risk. In this section, we’ll examine the key benefits of cloud browsers and we’ll look at some of the reasons why some users are choosing them.
In particular, there are two key advantages of using a cloud browser: the anonymity it offers, and protection against malicious code. These benefits are crucial to understanding why cloud browsers are especially popular among information security researchers and professionals in regulated industries.
Anonymity
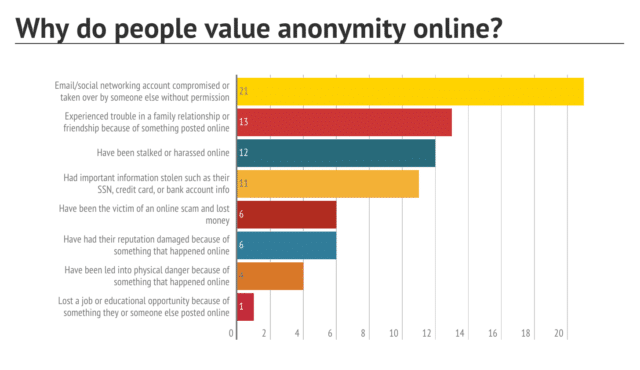
You might be wondering at this point what the big deal is when it comes to anonymity. In fact, in some countries where repressive regimes prevail, anonymity can be the difference between liberty and imprisonment. It shouldn’t be assumed that anonymity is always a cloak for malicious or criminal activity (though it certainly can be). It may also be necessary for citizens to express criticisms of an authoritarian government.
Of course, sometimes people just want to remain anonymous due to privacy concerns. Whether it’s hiding your data from advertisers or wanting your email content to remain hidden, there are plenty of reasons to want an anonymous online presence.
There are, of course, various tools which can help users maintain anonymity in their web browsing. These include virtual private networks (VPNs), which have been widely adopted by users, for instance, to protect them when using public Wi-Fi. However, some governments deny users access to VPNs and may log attempts to use them as suspicious.

There’s also incognito mode, but this doesn’t make a truly secure browser – it just reduces tracking cookies. Users may therefore have to take other measures to avoid being identified through their online activity. Cloud browsers can help to preserve user anonymity by serving as a proxy between an individual user and a target web server.
The user concerned navigates to a particular webpage via a cloud browser, and the browser requests that page from the target server before then processing the response. What is then displayed to the user is a reproduction of the requested page rather than the code itself; a real-time streamed image.
The owner of the webpage involved will not be able to ascertain where the request originated from, thus protecting the anonymity of the user at the other end. The only downside from the user’s standpoint is that the website response (and hence the browsing experience) might be slightly slower.
Protection against malicious code
Another important benefit of using a cloud browser is that it provides users with an important layer of protection from malicious code (such as malware). As we’ve discussed already, users frequently encounter security threats when browsing the web, whether through malicious or hacked websites, or dubious emails.
Remember what we said in the previous sub-section: cloud browsers act as a proxy between end-users and web servers (hence the term ‘remote browser’). The user does not, technically speaking, access websites themselves. Instead, the user views duplicates of them through a user interface.
This means that users browsing the web via a cloud browser don’t actually process the relevant website code on their own device. As a result, they also don’t process any malicious code that might be present: instead, this is absorbed by the intermediary cloud system. These systems also have robust and stringent security measures in place.

This is particularly helpful for businesses with a BYOD policy (bring your own device) in place as it can reduce the risk of threats making their way into their network.
Other benefits of cloud browsers
There are other benefits to using cloud browsers as well. For example, they provide employers with a greater degree of control over what their employees do online while they’re on company time. This has, needless to say, been a thorny challenge for businesses.
So for example, if an employer thinks staff are spending too much time on social media sites, watching streaming videos or playing interactive games, they could block access to the appropriate sites through making employees use a cloud browser which they control. This spares them the hassle of having to set up and maintain access lists via firewalls.
On top of this, businesses can effectively outsource responsibility for maintenance, capacity and scalability to high-quality, third-party providers and data centers. This simplifies matters for administrators by providing them with a single, overarching location from which they can exercise command and control.
With cloud browsers, there’s also less need for point solutions. This means that a lot of added functionality – such as data loss protection, endpoint security protection, domain name services and SSL inspection – can be scaled back.

How does a cloud browser work?
We’ve already discussed some of the functions of cloud browsers and how they work. In this section, we’ll explain things in a little more depth.
Cloud browsers combine a web browser application with a virtualised container to ensure isolation. This means that user commands (for instance, a google search) are separated from the user endpoint (your device), and are instead executed via a container.
All access to the internet is hosted in the cloud and controlled by a remote display protocol. All users have to do is use an installed app or open a browser-based portal to connect to the appropriate cloud service provider. In effect, this keeps users at arm’s length from the internet, allowing them to access content by proxy via remote servers.
If that’s a little bit too technical, the simple version is:
- You open an app or browser based portal
- This opens a ‘container’ which is hosted in the cloud, not your device
- All browsing happens within this virtual container
Choosing a cloud browser
There are various factors to consider when choosing a cloud provider. Perhaps the first thing you’ll need to think about is your budget. We’ve noted that there are freeware cloud browsers available, but some providers require a subscription fee.
You’ll need to assess the various options on the market and decide whether it’s worth paying for a cloud browser – and how much you’re prepared to pay. You should also look into whether the third-party provider stores any usage logs on its own system, as data residency could have security implications.
While VPN providers generally promise users that their usage data won’t be logged, cloud browser providers can be somewhat more opaque. Before you start using a particular cloud browser or commit yourself to anything, therefore, you should establish whether logs are kept and which jurisdiction they’re stored in.

This is a general rule you should also keep in mind when choosing other cloud-based services. The introduction of more stringent data protection regulations, such as GDPR, has meant added responsibility for businesses. But it’s in their own interest to keep their data, and that of their customers, away from prying eyes.
RingCentral Cloud Computing Security and Services
RingCentral offers a range of tough security protections to provide you with both security and peace of mind. As a one-stop solution for unified communications, RingCentral brings together team messaging, cloud-based phone calls, video conferencing and more. It goes without saying that you’ll be especially keen to keep all this totally secure.
With RingCentral, you can rest assured that you’ll have the benefit of robust security measures at every level: from the application itself to the servers it runs on, as well as RingCentral’s own business processes.
Your communications will be protected from interception by transport layer security and secure real-time transport protocol between all endpoints. RingCentral also offers other infrastructure safeguards, including firewalls and session border controllers, fraud analytics, intrusion-detection systems, multi-factor authentication and vulnerability scans.

Protecting your business with a cloud browser
It stands to reason that each business has its own specific security needs. There’s no single, foolproof solution that can suit the security requirements of every organisation, whatever its size and whatever its purposes.
Nevertheless, it is clear that cloud browsers can be part of the solution as far as cyber security and keeping your communications secure are concerned – and it’s essential that you take whatever steps you can (within reason) to ensure reliable protection.
A lot of people, in their private time and at work, are taking serious security risks – without even realising it – when they browse online. Those businesses that take proactive steps to minimise these risks are likely to see long-term benefits from doing so.
Originally published Feb 23, 2021, updated May 28, 2021

